Protecting user accounts using hashed passwords
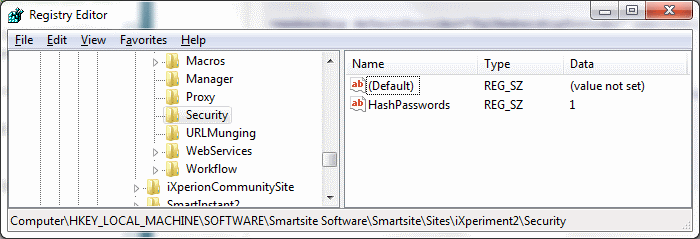
In Smartsite 5, the HashPasswords boolean setting can be set to 1 to skip (encrypted) password-saving altogether. Smartsite will then hash the passwords on update using the MD5 algorithm and compare the hash with the one generated when a user/visitor logs on:
The setting enforces that User- and Visitor passwords are not stored inside the site database. Instead, only an MD5 hash is stored.
No longer will anyone with access to the database be able to retrieve passwords and decrypt them.
In iXperion 1.4+, the feature has been reimplemented in the standard .NET Membership Provider (SqlMembershipProvider).
Config Editor
To enable the feature, use the Smartsite Config Editor. Open the appropriate site, select Unlock and switch to Advanced Mode (using View menu). Then in the right pane within the Security section you have the option to set the Password Format. Select Hashed as the new value.
When saving this change, the Config Editor will update the passwordFormat attribute of the Sql Membership Provider within the web.config:
| XML |
|
|---|---|
<membership defaultProvider="SqlMembershipProvider" userIsOnlineTimeWindow="15">
<providers>
<clear />
<add applicationName="Smartsite"
name="SqlMembershipProvider"
type="Smartsite.Security.Authentication.SqlMembershipProvider, Smartsite.Security"
enablePasswordRetrieval="true"
enablePasswordReset="true"
passwordFormat="Hashed"
requiresQuestionAndAnswer="false"
writeExceptionsToEventLog="true"
/>
<!-- optionally other providers -->
</providers>
</membership>
|
|
It will also check/set the above mentioned HashPasswords registry setting.
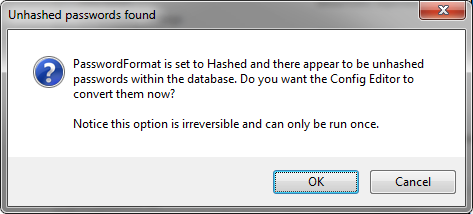
Furthermore, when the Password Format is set to Hashed, the Config Editor will verify the passwords already stored within the database. If not all passwords are in hashed format, the Config Editor offers the option to convert all passwords to hashed format: