Multi-domaining support revisited
As stated within the article Configuring Multiple Active Directory domains, the Smartsite Active Directory Membership Provider already had built-in multi-domain support. And as of iXperion release 1.2, support for LDAP servers, such as Novell e-Directory, has been added as well using the Smartsite LDAP Membership Provider.
To be able to use the same membership provider and the same configuration settings for the cms manager, iXperion release 1.2 also introduced the new logonhandler SixSecurity.LDAP. This class uses COM interop to invoke the LDAP membership provider to handle authentication requests.
However, one thing was still missing: multi-domain support for the cms manager using the logonhandler SixSecurity.LDAP. Well, as of iXperion 1.4 build 3 this is supported as well. This article describes the configuration needed for this scenario.
Membership providers
In this multi-domaining example configuration, it is assumed that there are two (seperate) Active Directory domains with which the site must be able to connect. In that case, for each domain a seperate membership provider must be configured as well:
| XML |
|
|---|---|
<add applicationName="Smartsite" name="domain1Provider" type="Smartsite.Security.Authentication.ActiveDirectoryMembershipProvider, Smartsite.Security" connectionStringName="domain1ProviderConnection" connectionUsername="username@domain1" connectionPassword="password" settingsSectionName="domain1Provider.Configuration" /> <add applicationName="Smartsite" name="domain2Provider" type="Smartsite.Security.Authentication.ActiveDirectoryMembershipProvider, Smartsite.Security" connectionStringName="domain2ProviderConnection" connectionUsername="username@domain2" connectionPassword="password" settingsSectionName="domain2Provider.Configuration" /> |
|
Both these membership providers uses their own connection string, referenced by name using the connectionStringName attribute:
| XML |
|
|---|---|
<connectionStrings> <add name="domain1ProviderConnection" connectionString="LDAP://DOMAIN1" /> <add name="domain2ProviderConnection" connectionString="LDAP://DOMAIN2" /> </connectionStrings> |
|
Configuration Sections
Since the LDAP membership provider is used for the cms manager, it is required to specify a Search Base. This setting can be specified using a configuration section of type Smartsite.Security.ActiveDirectoryConfigurationSection, Smartsite.Security. However, for each domain a different Search Base must be provided. Therefore, as of iXperion 1.4 build 3, each membership provider can specify its own configuration section using the settingsSectionName attribute (which is already included in the examples above).
(In previous versions, this would have been the Smartsite.ActiveDirectoryConfiguration section when using Active Directory or Smartsite.LDAPConfiguration section when using LDAP; for backwards compatibility these names are used as default when settingsSectionName has not been specified.)
An example of the configuration sections for both providers is shown below.
| XML |
|
|---|---|
<domain1Provider.Configuration> <settings> <add name="SmartsiteAccessGroup" value="SmartsiteAccessGroup" /> <add name="ManagerAccessGroup" value="ManagerAccessGroup" /> <add name="StoreFullyQualifiedLoginName" value="true" /> <add name="SearchBase" value="DC=domain1,DC=lan" /> <add name="DatabaseId" value="manager" /> </settings> <membershipMappings> <add name="mm1" domain="domain1" /> <add name="mm2" domain="domain1.lan" /> </membershipMappings> </domain1Provider.Configuration> <domain2Provider.Configuration> <settings> <add name="SmartsiteAccessGroup" value="iXperionAccessGroup" /> <add name="ManagerAccessGroup" value="iXperionManagerAccessGroup" /> <add name="StoreFullyQualifiedLoginName" value="true" /> <add name="SearchBase" value="DC=domain2,DC=com" /> <add name="DatabaseId" value="manager" /> </settings> <membershipMappings> <add name="mm3" domain="domain2" /> <add name="mm4" domain="domain2.com" /> </membershipMappings> </domain2Provider.Configuration> |
|
As you might have noticed, because each membership provider has its own configration section, it's no longer required to use the same group names on each domain for the Smartsite- and Manager Access groups.
Because ASP.NET needs to know beforehand how to process each configuration section within the web.config, the configSections element must be adjusted as well:
| XML |
|
|---|---|
<configSections> <!-- other section definitions --> <section name="domain1Provider.Configuration" type="Smartsite.Security.ActiveDirectoryConfigurationSection, Smartsite.Security" /> <section name="domain2Provider.Configuration" type="Smartsite.Security.ActiveDirectoryConfigurationSection, Smartsite.Security" /> </configSections> |
|
SwitchProviderOnSupportedDomainsList release setting
Multi-domain support within previous versions relied on the providerName attribute within the membershipMappings element. The default provider serves as a proxy and checks the membershipMappings element to match the user's domainname with one of the providers, based on the providerName attribute.
As of iXperion 1.4 build 3, it is preferred (and when multi-domain support within the cms manager is needed, it is required) to give each membership provider its own configuration section and therefore each membership provider has its own list of domains.
The default provider still serves as a proxy, however finding the appropriate membership provider can now be achieved by iterating the membership providers and evaluate the domains listed within its own membershipMappings element against the user's domainname. This (preferred) behaviour will be applied when the release setting SwitchProviderOnSupportedDomainsList has been set to true. (Notice that for new sites, based on the EmptySix template, this release setting will be true by default, since it's included in the default smartise.config.)
Config Editor
To configure multi-domain support, it is required to add and/or change four elements within the web.config:
- Add or change membership provider for a specific domain.
- Configure connectionString for the domain within the connectionStrings element.
- Create or update configuration section for a specific domain.
- Make sure the configuration section's name is defined within the configSections element.
But it would be a lot easier to use the Config Editor that ships with 1.4 build 3, because it has built-in support to configure multiple membership providers, each having their own configuration section.
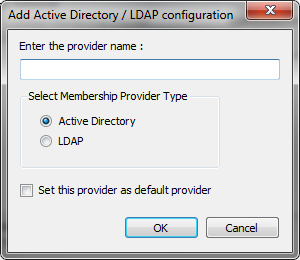
When adding a new Active Directory configuration, it asks for a provider name and type, and then adds all the necessary configuration elements to the web.config.